Course description
This course will explore types of security threats, both digital and physical. It starts with protecting digital information and then types of malware such as viruses, worms, trojans and phishing. It will finish with Storage and Backups.
Prerequisites
There are no prerequisites.
Learning Paths
This course is part of the following LearnNowOnline SuccessPaths™:
Security Awareness
Meet the expert
As a certified Microsoft Instructor, Ken has focused his career on various security aspects of computer and network technology since the early 1980s. He has offered a wide variety of IT training and high level consulting projects for Fortune 500 companies globally. Through the course of his extensive career, he has taught a full line of Microsoft, CompTIA, Cisco, and other high level IT Security curricula.
Course outline
Protection and Malware
Protecting Digital Information Part 1 (30:06)
- Introduction (00:10)
- Protecting Digital Information (02:14)
- Types of Backups (05:24)
- Backup Strategies (04:25)
- What to Backup (02:27)
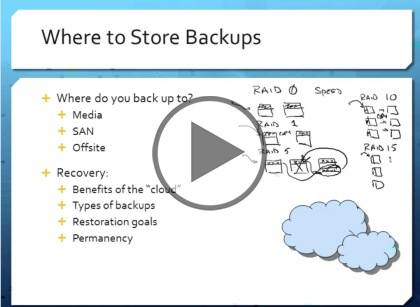
- Store Backups (02:07)
- Where to Store Backups (02:26)
- How to Perform Backups (02:21)
- Demo: Backup Windows (04:23)
- Virtualization Solutions (03:55)
- Summary (00:08)
Protecting Digital Information Part 2 (28:06)
- Introduction (00:08)
- Commonly-Used Programs (01:37)
- Backup Management Practices (03:21)
- Passwords (04:51)
- Demo: Hash Cracking (05:22)
- Password Management (04:48)
- Password Management (Cont.) (01:55)
- Length and Complexity (01:12)
- Password Management (Cont. Again) (01:30)
- AAA (03:08)
- Summary (00:08)
Malware Part 1 (25:51)
- Introduction (00:08)
- Introduction (00:35)
- Basic Definitions (07:04)
- What to Look for (05:41)
- How You Can Get Infected (03:42)
- Software Detection (08:31)
- Summary (00:08)
Malware Part 2 (18:55)
- Introduction (00:08)
- Hardware Detection (02:16)
- Cloud Detection (03:32)
- Know the Extensions (03:23)
- Demo: Understanding File Extensions (06:37)
- What to Install (02:48)
- Summary (00:08)