Certified Virtualization Security Expert, Part 4 of 6: PenTest Tools and DMZ
with experts Duane Anderson, Tim Pierson
Course description
What are the tools of a penetration test? This course will answer that as well as cover vulnerability assessment, password cracking, how to disable auditing, rootkits and alternate data streams. Then it progress to three configurations of DMZs, hardening and isolating, layer 2 security options and separation of duties. Finally threats like SSL renegotiation and web access vulnerabilities will round out the course.
Prerequisites
This is part 4 of the series.
Learning Paths
This course will help you prepare for the following certification and exam:
Certified Virtualization Security Expert
Meet the experts
Duane has been working in the IT industry for over two decades. He has primarily focused on security related matters such as
Penetration Testing and Forensics. He has appeared as an expert witness
in multiple court hearings on IT related matters. Duane has worked for
or with most US and some foreign military branches, U.S government
agencies, banking and regulatory industries and Fortune 500 companies.
Duane contributed to the coordination and execution of IT
counter-hacking & security courses for the US Marine Corps, US Army,
US Air Force, U.S. Treasury, Sprint, IBM, Washington Mutual and Service
Canada.
Tim one of the World’s leading trainers in technology,
networks, virtualization and, applications. He has been a technical trainer and consultant for security and virtualization for the past 25 years. He has 29 industry technical certifications from CISCO, Microsoft and Novell. Tim has been a noted speaker at many industry events such as Infosec World 2010, Innatech and GISSA. He is a contributing author of VMware vSphere and Virtual Infrastructure Security Securing ESX in the Virtual Environment.
networks, virtualization and, applications. He has been a technical trainer and consultant for security and virtualization for the past 25 years. He has 29 industry technical certifications from CISCO, Microsoft and Novell. Tim has been a noted speaker at many industry events such as Infosec World 2010, Innatech and GISSA. He is a contributing author of VMware vSphere and Virtual Infrastructure Security Securing ESX in the Virtual Environment.
Course outline
Penetration Testing Tools
Vulnerability Scanners (40:24)
- Introduction (00:54)
- BackTrack4 (01:10)
- Vulerability Scanners (00:28)
- Nessus (01:12)
- Nessus Report (00:57)
- Saint (01:16)
- Saint Sample Report (00:42)
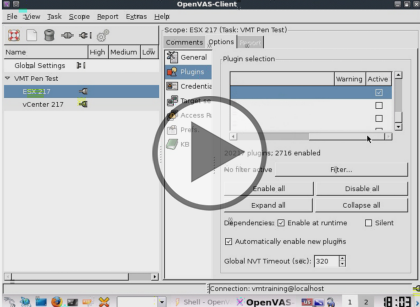
- OpenVAS (01:02)
- OpenVAS Infrastructure and Client (03:31)
- Demo: OpenVAS (05:29)
- Demo: Connecting to the Server (03:14)
- Demo: New Connections (05:19)
- Demo: Perform a Scan (05:37)
- Demo: Scan Continued (02:19)
- Demo: Scan Report (06:58)
- Summary (00:08)
Password Cracking (24:22)
- Introduction (00:08)
- Windows Password Cracking (02:48)
- SysKey and Cracking Techniques (03:49)
- Rainbow Tables (01:29)
- Disabling Auditing (01:10)
- Clearing the Event Log (00:45)
- NTFS Alternate Data Stream (02:14)
- Stream Explorer (00:39)
- Encrypted Tunnels (01:37)
- Port Monitoring Software (01:30)
- Rootkits (02:21)
- Utilizing Tools (01:05)
- Defense in Depth (02:17)
- Meterpreter (01:41)
- VASTO (00:34)
- Summary (00:08)
Pen Testing Tools (21:13)
- Introduction (00:08)
- VASTO Modules (03:17)
- Fuzzers (01:57)
- Saint (00:55)
- Core Impact Overview (01:35)
- Core Impact (01:39)
- Tool Exploits from NVD (01:43)
- Wireshark and TCP Stream Reassembling (02:28)
- ARP Cache Poisoning (02:07)
- ARP Cache Poisoning in Linux (01:24)
- Cain and Abel (02:37)
- Ettercap (01:10)
- Summary (00:08)
DMZs and Attack Vectors
Virtualized DMZ (25:11)
- Introduction (00:38)
- Virtualized DMZ Networks (04:36)
- Three Typical Virtualized DMZ Configurations (03:20)
- Partially-Collapsed DMZ with Virtual Separation (02:02)
- Fully-Collapsed DMZ (03:06)
- Best Practices (03:27)
- Network Labeling (01:24)
- Layer 2 Security Options on Virtual Switches (01:09)
- Enforce Separation of Duties (02:03)
- ESX Management Capabilities (03:14)
- Summary (00:08)
Common Attack Vectors (22:35)
- Introduction (00:08)
- Common Attack Vectors (01:06)
- How Fake Certificate Injection Works (01:28)
- Generic TLS Renegotiation Prefix Injection (05:27)
- Test Vulnerabilities (01:10)
- Vulnerability Requirements (01:50)
- Generic Example (02:12)
- Patched Server with DIsabled Recognition (00:43)
- Keeping Up to Speed (01:28)
- SchmooCon 2010: Timeline (01:16)
- SchmooCon 2010: Identification (01:04)
- SchmooCon 2010: Server Log In (00:27)
- SchmooCon 2010: Vulnerability (01:06)
- SchmooCon 2010: Redirection Proxy (00:24)
- SchmooCon 2010: Vulnerable Versions (00:34)
- SchmooCon 2010: Gueststealer (01:57)
- Summary (00:08)