Certified Virtualization Security Expert, Part 3 of 6: Penetration Testing 101
with experts Duane Anderson, Tim Pierson
Course description
To be secure you have to think like a hacker. This course covers penetration testing, how much hacks cost, evolving threats, information gathering, scanning, enumeration and finishes with tools that hackers and you can utilize to gather information.
Prerequisites
This is part 3 of the series.
Learning Paths
This course will help you prepare for the following certification and exam:
Certified Virtualization Security Expert
Meet the experts
Duane has been working in the IT industry for over two decades. He has primarily focused on security related matters such as
Penetration Testing and Forensics. He has appeared as an expert witness
in multiple court hearings on IT related matters. Duane has worked for
or with most US and some foreign military branches, U.S government
agencies, banking and regulatory industries and Fortune 500 companies.
Duane contributed to the coordination and execution of IT
counter-hacking & security courses for the US Marine Corps, US Army,
US Air Force, U.S. Treasury, Sprint, IBM, Washington Mutual and Service
Canada.
Tim one of the World’s leading trainers in technology,
networks, virtualization and, applications. He has been a technical trainer and consultant for security and virtualization for the past 25 years. He has 29 industry technical certifications from CISCO, Microsoft and Novell. Tim has been a noted speaker at many industry events such as Infosec World 2010, Innatech and GISSA. He is a contributing author of VMware vSphere and Virtual Infrastructure Security Securing ESX in the Virtual Environment.
networks, virtualization and, applications. He has been a technical trainer and consultant for security and virtualization for the past 25 years. He has 29 industry technical certifications from CISCO, Microsoft and Novell. Tim has been a noted speaker at many industry events such as Infosec World 2010, Innatech and GISSA. He is a contributing author of VMware vSphere and Virtual Infrastructure Security Securing ESX in the Virtual Environment.
Course outline
Penetration Testing
Exploits and Malware (31:29)
- Introduction (00:18)
- Benefits of a Penetration Test (03:12)
- The Cost of Hacks (02:07)
- Cost of a Hack: Example (01:29)
- Current Issues: Malware (04:01)
- Zombies (03:20)
- Current Issues: Zombies (02:41)
- Current Issues: Botnets (02:29)
- Stolen Information (01:57)
- Current Issues: Social Engineering and Exploits (03:16)
- Chained Exploit Example (02:58)
- Gozalez Indictment (03:27)
- Summary (00:08)
Penetration Testing (40:40)
- Introduction (00:08)
- The Evolving Threat (05:28)
- Methodology for Pen Testing/Ethical Hacking (06:21)
- Penetration Testing Methodologies (01:42)
- Different Types of Penetration Tests (02:34)
- Website Review (01:22)
- Demo: Security Websites (04:28)
- Demo: More Security Websites (08:39)
- Management Errors (02:47)
- VMware Concerns (06:58)
- Summary (00:08)
Performing Reconnaissance
Footprinting (28:25)
- Introduction (00:31)
- Methods of Obtaining Information (01:11)
- Footprinting (01:44)
- Footprinting Tools (01:03)
- Maltego GUI (02:35)
- Demo: Maltego (03:49)
- Demo: Maltego Transforms (08:42)
- FireCAT (01:58)
- Demo: FireCAT (06:41)
- Summary (00:08)
Port Scanning (44:11)
- Introduction (00:08)
- FireFox Fully Loaded (00:55)
- Google Hacking (01:26)
- Advanced Query Operators (02:10)
- Google Continued (01:02)
- Shodan (02:11)
- Demo: Shodan (06:15)
- Port Scanning (02:59)
- Popular Port Scanning Tools (01:20)
- ICMP Disabled (01:42)
- TCP Connect Port Scan and NMAP (02:16)
- Half-Open Scan, Firewalled Ports, and UDP Ports (03:37)
- Demo: (00:42)
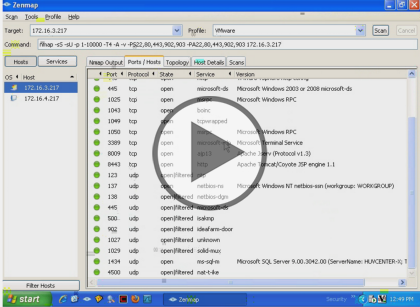
- Demo: Port Scanning wiht NMAP (04:29)
- Demo: Perform Scan (04:53)
- Demo: Discovered Ports (03:10)
- Demo: Reading Output (04:41)
- Summary (00:08)
Enumeration (42:14)
- Introduction (00:08)
- UDP Port Scan (00:29)
- Enumeration (01:49)
- Banner Grabbing (02:22)
- DNS Enumeration (01:04)
- Zone Transfers (02:33)
- Backtrack DNS Enumeration (01:05)
- Active Directory Enumeration (01:36)
- LDAPMiner (01:00)
- Null Session (01:41)
- Syntax for a Null Session (01:13)
- Enumeration with Cain and Abel (02:14)
- NAT Dictionary Attack Tool (01:02)
- THC-Hydra (00:47)
- Injecting Abel Service (00:59)
- Demo: Cain and Abel (06:10)
- Demo: ARP Poisoning (04:28)
- Demo: Certificates (04:45)
- Demo: Modify Port Function (06:33)
- Summary (00:08)