Certified Virtualization Security Expert, Part 1 of 6: Reaffirming Knowledge
with experts Duane Anderson, Tim Pierson
Course description
This course will start by taking a look at virtual components, ESX networking components, switches, vswitch and physical switch. It will then discuss spanning tree protool, vswitch isolation, virtual ports, vlans, load balancing, failover configuration, managing a virtual network, encryption and certificates and finish up with the Linux file system.
Prerequisites
This is part 1 of the series
Learning Paths
This course will help you prepare for the following certification and exam:
Certified Virtualization Security Expert
Meet the experts
Duane has been working in the IT industry for over two decades. He has primarily focused on security related matters such as
Penetration Testing and Forensics. He has appeared as an expert witness
in multiple court hearings on IT related matters. Duane has worked for
or with most US and some foreign military branches, U.S government
agencies, banking and regulatory industries and Fortune 500 companies.
Duane contributed to the coordination and execution of IT
counter-hacking & security courses for the US Marine Corps, US Army,
US Air Force, U.S. Treasury, Sprint, IBM, Washington Mutual and Service
Canada.
Tim one of the World’s leading trainers in technology,
networks, virtualization and, applications. He has been a technical trainer and consultant for security and virtualization for the past 25 years. He has 29 industry technical certifications from CISCO, Microsoft and Novell. Tim has been a noted speaker at many industry events such as Infosec World 2010, Innatech and GISSA. He is a contributing author of VMware vSphere and Virtual Infrastructure Security Securing ESX in the Virtual Environment.
networks, virtualization and, applications. He has been a technical trainer and consultant for security and virtualization for the past 25 years. He has 29 industry technical certifications from CISCO, Microsoft and Novell. Tim has been a noted speaker at many industry events such as Infosec World 2010, Innatech and GISSA. He is a contributing author of VMware vSphere and Virtual Infrastructure Security Securing ESX in the Virtual Environment.
Course outline
Introduction to Network Security
Introduction to Networking (33:02)
- Introduction (00:26)
- How Virtual Ethernet Adapters Work (03:00)
- How Virtual Switches Work (02:26)
- VMSafe (01:58)
- Current VMSafe Partners (00:58)
- Virtual Switch vs. Physical Switch (00:53)
- Cam Tables (06:43)
- Spanning Tree Protocol (01:48)
- Virtual Ports (01:18)
- Uplink Ports and Port Groups (02:19)
- Uplinks (00:25)
- VIrtual Switch Correctness (01:17)
- VLANs in VMWare Infrastructure (02:29)
- Failover Configuration (01:46)
- Virtual Machine Operation (05:01)
- Summary (00:08)
Virtual Network Security (27:28)
- Introduction (00:08)
- Forged Transmits (03:10)
- Managing the Virtual Network (02:43)
- Symmetric vs. Asymmetric Encryption (07:49)
- Demo: Virtual Switch Security Settings (05:09)
- Hashes (04:58)
- Demo: Hashes (03:20)
- Summary (00:08)
Remote Access and the Linux File System
Remote Access (47:45)
- Introduction (00:08)
- Digital Signatures (04:16)
- Breaking SSL Traffic (07:12)
- VMTraining's Physical Setup (04:37)
- Demo: Connecting into DRAC Client (05:38)
- Demo: DRAC Console (02:00)
- Demo: PuTTy (05:45)
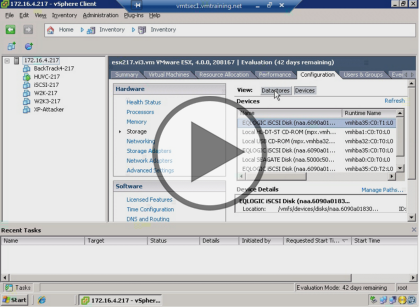
- Demo: vSphere Client (05:25)
- Demo: Virtual Center in vSphere Client (01:50)
- Demo: ARP Injections (04:45)
- Demo: ARP Cache Poisoning (03:47)
- Introduction to Linux (02:07)
- Summary (00:08)
Linux (46:44)
- Introduction (00:08)
- File System Structure (04:35)
- Kernel (01:00)
- Processes (00:58)
- Processes Continued (01:23)
- Staring and Stopping Processes (01:39)
- Interacting with Processes (01:15)
- Storing Account and Group Information (01:57)
- Password and Shadow File Formats (01:15)
- Accounts and Groups (03:03)
- Linux and UNIX Permissions (05:10)
- Demo: Introduction to Linux (03:47)
- Demo: Get IP Address (06:09)
- Demo: Configuring and Navigating Linux (02:25)
- Demo: Navigating Linux (07:20)
- Set UID Programs, Logs, and Editing (04:22)
- Summary (00:08)