Course description
Security is becoming a concern of everyone. In this course we will dive into some of the features in SQL Server 2012 that relate to security. We will take a look at the encryption keys that SQL Server creates and uses, along with certificates, to protect everything from cell level data to entire databases. Then we will see how Transparent Data Encryption can help to quickly bring a database into compliance with most regulations and requirements. We will also see what exactly is required to move an encrypted database to a new server without losing any data. User defined server roles is a new SQL 2012 feature that makes administration easier when it comes to security. We will go over this and even create our own Server Role for members of the data team. Next we will look at ways to protect individual objects in your databases using security permissions and show how, as the DBA, you can test your configuration using the Execute As capabilities of SQL Server. Next we are going to look into the Resource Governor and Policy Based management. We will go through the Components of the Resource Governor and show how you can use this great feature of Enterprise edition to classify incoming connections and identify specific users or groups that are using excessive resources on the server. We will then look at the Policy Group Management feature of SQL Server. We will create policies that check and enforce naming conventions and ensure proper backups are being configured on your servers.
Prerequisites
This course assumes that students have working experience with SQL Server 2005 or 2008; basic relational database concepts (e.g., tables, queries, and indexing); general knowledge of XML, Transact-SQL, and a fundamental understanding of networking and security concepts.
Learning Paths
This course is part of the following LearnNowOnline SuccessPaths™:
SQL Server Administrator
Meet the expert
Chris Bell, MCITP, is an 18-year SQL Server veteran for both business intelligence and application development providing solutions for businesses, organizations, and individuals. He is the founder and CEO of WaterOx Consulting, Inc., a provider of remote SQL Server consulting and services. Chris is also the founder and current President of the Washington DC chapter of PASS and a member of the Board of Directors for CPCUG. Chris also frequently attends and presents at PASS events around the country, sharing his passion for all things SQL Server. In 2012, Chris was one of 5 finalists in the world for Red Gate’s Exceptional DBA Award.
Course outline
Security
Encryption Keys (16:49)
- Introduction (00:28)
- Database Encryption Keys (01:28)
- Managing Encryption (00:34)
- Service Master Key (00:41)
- Backup the SMK (01:00)
- Restore the SMK (01:10)
- Alter the SMK (00:57)
- Create a Database Master Key (00:37)
- Backup the DMK (00:49)
- Restore a DMK (01:31)
- Alter a DMK (01:01)
- Demo: Backup Master Keys (00:58)
- Demo: Alter Master Key (01:26)
- Demo: Create Master Key (03:44)
- Summary (00:19)
Transparent Data Encryption (15:02)
- Introduction (00:42)
- Certificates and Database Keys (00:34)
- Transparent Data Encryption (00:39)
- TDE - Pros & Cons (01:38)
- TDE - Restoring the Backup (00:34)
- Demo: Enable TDE (03:19)
- Demo: Disable Encryption (00:46)
- Demo: Moving TDE (03:28)
- Demo: Backup TDE (03:00)
- Summary (00:19)
Server Roles (20:01)
- Introduction (00:32)
- User Defined Server Roles (00:40)
- Demo: Creating Roles (03:37)
- Protecting Objects (01:02)
- Grant Permissions (00:31)
- Deny Permissions (00:28)
- Revoke Permissions (00:31)
- Execute As (01:09)
- Demo: Built-In Permissions (05:44)
- Demo: Testing Permissions (05:20)
- Summary (00:23)
Resource Management
Resource Governor (19:49)
- Introduction (00:36)
- Resource Governor (04:18)
- Demo: Resource Governor (05:10)
- Demo: Assigning Functions (03:02)
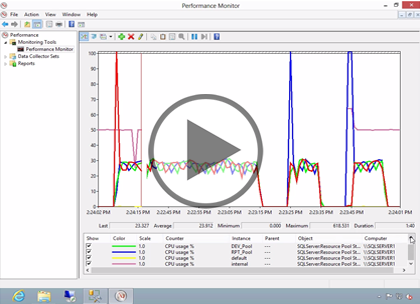
- Demo: Performance Monitor (06:22)
- Summary (00:18)
Policy-Based Management (39:29)
- Introduction (00:28)
- Policy-Based Management (06:48)
- Central Management Server (00:32)
- Demo: Policy Management (05:21)
- Demo: Create Policy (04:11)
- Demo: Enforcing Policy (04:04)
- Demo: Recovery Model (05:01)
- Demo: Evaluating Policies (03:33)
- Demo: Importing Policies (05:12)
- Demo: Policy Violations (04:02)
- Summary (00:13)