Course description
Which operating system are you best with? Do you prefer Linux over Windows, Windows over a Mac or a combination of the three? We are going to take a look at Operating System forensics so you can see in inner workings so we can find potential evidence. We will look at volatile and non-volatile data, how deal with both and techniques we can use to collect it to start off with. Once we understand data, then the operating systems will be picked apart so we, as investigators, know where to look for information. Afterwards, maybe you will change your mind from your favorite to different operating systems. This course is part of a series covering the EC-Council Computer Hacking Forensic Investigator (CHFI).
Prerequisites
Recommended:
Understanding of networking; How data flows from source and destination
Computer security basics such as passwords, encryption and physical security
Basic understanding of computing and computer systems
Experience with various operating systems
Learning Paths
This course will help you prepare for the following certification and exam:
Computer Hacking Forensic Investigator
Meet the expert
David Bigger is the lead trainer at Bigger IT Solutions. He has been information technology for a little over 20 years and has been training all over the US. He has worked with companies like US Military, Lockheed Martin, General Dynamics, Dominos Pizza, University of Utah and Expedia
Course outline
Data and Forensics
Windows Volatile Data (23:21)
- Introduction (00:26)
- Operating System Forensics (01:13)
- Windows Volatile Data (01:26)
- Windows Volatile Data Examples (00:50)
- System Time and Open Files (01:49)
- Shares and Command History (02:09)
- Clipboard Contents and Logged On Users (02:52)
- Mapped Drives and Process Information (02:33)
- Network Information (02:10)
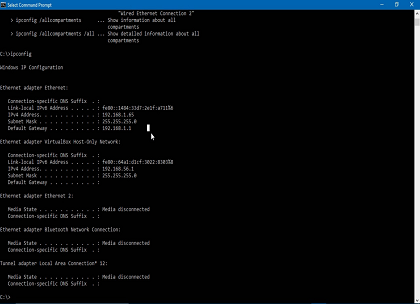
- Demo for Network Information (00:17)
- Demo: Network Information, Ipconfig (02:57)
- Demo: Network Information, Netstat (04:17)
- Summary (00:16)
Windows Non-Volatile Data (31:08)
- Introduction (00:26)
- Windows Non-Volatile Data (04:49)
- Event Logs (04:33)
- Registry Settings (04:28)
- Registry Information Available (02:17)
- Registry and the USB (01:36)
- Browser Information (01:04)
- Chrome Browser Information (01:51)
- Edge Browser Information (01:28)
- Firefox Browser Information (01:05)
- Thumbcaches (02:41)
- Slack Space (01:56)
- Hidden Partitions (01:22)
- The Page File (01:06)
- Summary (00:17)
Linux Forensics (13:58)
- Introduction (00:19)
- Linux Forensics (00:49)
- Linux Log Files (04:15)
- Other Linux Files (01:01)
- Linux Shell Commands (05:50)
- Collecting Linux Network Information (01:24)
- Summary (00:17)
Mac Forensics (08:30)
- Introduction (00:18)
- Mac Forensics (01:06)
- Mac Log Files (01:12)
- Evidence on a Mac (02:50)
- Safari (00:42)
- Viewing Evidence on a Mac (02:02)
- Summary (00:17)