Course description
Dive into data acquisition to discover the differences between live and static acquisitions, as well as to learn about volatile data, or the data that should be acquired first once a system has been determined to be a crime scene. Additionally, explore the various tools and the necessary hardware and software required to carry out a successful investigation. Following an exploration of data acquisition, take a closer look at anti-forensics to understand the techniques criminals may use to make your acquisition more difficult including encryption and file deletion. Then, learn about the countermeasures that can be implemented to overcome acquisition obstacles including password crackers and undelete utilities. This course is part of a series covering the EC-Council Computer Hacking Forensic Investigator (CHFI).
Prerequisites
Recommended:
Understanding of networking; How data flows from source and destination
Computer security basics such as passwords, encryption and physical security
Basic understanding of computing and computer systems
Experience with various operating systems
Learning Paths
This course will help you prepare for the following certification and exam:
Computer Hacking Forensic Investigator
Meet the expert
David Bigger is the lead trainer at Bigger IT Solutions. He has been information technology for a little over 20 years and has been training all over the US. He has worked with companies like US Military, Lockheed Martin, General Dynamics, Dominos Pizza, University of Utah and Expedia
Course outline
Data Acquisition and Anti-Forensics
Data Acquisition (16:48)
- Introduction (00:26)
- Data Acquisition (03:25)
- Volatile Data (02:14)
- Non-Volatile Data (01:05)
- Do We Need Copies? (01:11)
- Copies or Duplicates (01:39)
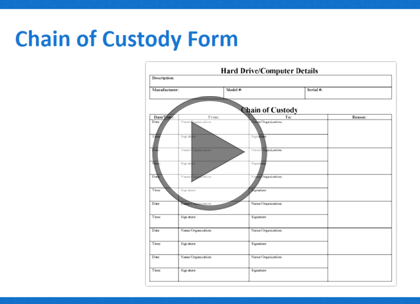
- Chain of Custody (00:44)
- Chain of Custody Form (00:45)
- Forensic Tools (00:48)
- Software Forensic Tools for Acquisition (01:36)
- Hardware Forensic Tools for Acquisition (02:21)
- Summary (00:29)
Live Acquisition (19:30)
- Introduction (00:28)
- Live Acquisition (04:13)
- Live Acquisition Common Items (02:23)
- Which Volatile Data First (01:08)
- Live Acquisition Steps (02:32)
- Live Acquisiton Tools (00:51)
- Live Acquisition Common Mistakes (04:43)
- Locard's Exhchange Principle (02:46)
- Summary (00:22)
Static Acquisition (16:37)
- Introduction (00:29)
- Static Acquisition (03:32)
- Write Blockers (01:20)
- Destination Media (01:10)
- Static Acquisition Tools (00:23)
- Acquisition Methods (00:24)
- Disk to Disk (00:50)
- Disk to Image (00:58)
- Static Acquisition Image Formats (00:34)
- Format (02:38)
- Sparse and Logical Acquisition (01:17)
- Are the Copies Good? (02:37)
- Summary (00:20)
Anti-Forensics (11:56)
- Introduction (00:23)
- Anti-Forensics (01:37)
- Why Do They Use Anti-Forensics? (01:55)
- Techniques Used (05:04)
- Case Study (01:22)
- Tools and Techniques Used (01:17)
- Summary (00:16)
Techniques (15:08)
- Introduction (00:21)
- Techniques Used: An In-Depth Look (00:30)
- Password Protection (03:11)
- Password Cracking Techniques (02:35)
- Deleting Files (04:24)
- Encryption (01:15)
- Rootkits (00:49)
- Rootkit Types (01:40)
- Summary (00:20)
Countermeasures (07:11)
- Introduction (00:30)
- Countermeasures (03:40)
- Challenges (00:01)
- Challenges (02:41)
- Summary (00:17)