Course description
There is a lot of confusion, even amongst security professionals, as to what makes a security analyst. Explore what it really means to be a security analyst by examining what CBK (Common Body of Knowledge) a security analyst might possess, as well as the challenges and concerns a security analyst may face related to managing corporate and government frameworks and infrastructures. Most information security conversations that happen at an analyst’s level have to do with one or more of three things: policies, procedures, or security controls. Discover a new way of looking at policies, procedures, and security controls, and find out how they’re fully connected to risk assessment and information security awareness.
Prerequisites
In order to maximize you leaning experience when taking this course, the following prerequisites are highly recommended:
Security + Certification, knowledge of CEH (Certified Ethical Hacker), knowledge of
CHFI (Computer Hacking Forensic Investigator) and the CBK (Common Body of Knowledge) associated with the CISSP and CISA certifications are also very helpful.
Meet the expert
Don Bowers has been in the computer industry for over 36 years as a database programmer and an information systems and security analyst. Don’s primary focus over the last 10 years has been in the area of information security and digital forensics. Don currently serves as an Assistant Professor and the Program Chair for the Cybersecurity program at the College of Western Idaho. As well as being an associate professor Don also holds the distinction of being a Certified EC-Council Instructor. Don holds several industry certifications including MCITP Enterprise, MCSE + Security, CISSP, CISA, CEH, CHFI, ECSA (EC-Council Security Analysis), LPT (Licensed Penetration Tester) and ACE (AccessData Certified Examiner).
Course outline
Security Analyst and the Threat Landscape
What is a Security Analyst (43:36)
- Introduction (00:29)
- What is a Security Analyst (08:54)
- Security Analyst, The Landscape (08:34)
- Security Analyst, Certifications (05:00)
- Security Concerns and Challenges (04:48)
- Network Intrusion Concerns (05:58)
- Greatest Challenges of Information Security (09:22)
- Summary (00:29)
Threat Landscape (17:05)
- Introduction (00:32)
- Threat Landscape (04:59)
- Demo: Security Web Sites (04:49)
- Threat Landscape, The Hackers (06:18)
- Summary (00:26)
Policies, Procedures, and Risk
Policies and Procedures (36:06)
- Introduction (00:23)
- Security Policies and Procedures (08:13)
- Security Policy Basics (02:47)
- Security Policy Examples (02:45)
- How to Create Security Policies (07:07)
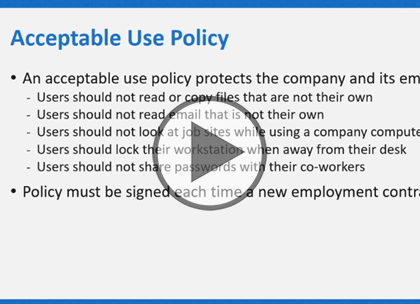
- Acceptable Use Policy (05:30)
- Being the Smartest Person in the Room (03:43)
- The Smartest Person, CSC 7 - CSC 20 (04:57)
- Summary (00:37)
Risk Assessment (24:17)
- Introduction (00:38)
- Risk Assessment and Security Awareness (06:18)
- Simple Risk Assessment Equation (04:19)
- Steps in Assessing and Evaluating Risk (04:13)
- Vulnerability Assessment Tools (03:08)
- Risk Assessment Answers Seven Questions (01:55)
- Security Awareness (03:08)
- Summary (00:34)